Secure code: secure coding practices owasp for 2026
Secure coding practices, especially those championed by OWASP, aren't just a set of rules. Think of them as a shared blueprint for building software that can actually withstand attacks. It's about constructing applications securely from the very first line of code, not just patching them up at the end.
Why Secure Coding Is Non-Negotiable in the Age of AI

We're in a strange new world of software development. AI coding assistants let us ship features faster than ever, but that speed has a serious downside: a massive blind spot for security. The rate at which AI generates code is simply too fast for old-school, manual security reviews to keep up.
The data on this is pretty shocking. A 2026 study that dug into AI-generated code found that a staggering 25.1% of code samples had at least one confirmed vulnerability. That’s a huge problem when tools in Cursor, VS Code, or Claude are pumping out code nonstop. You can read more about this on AppSec Santa's site.
This reality exposes a fundamental flaw in the old way of doing things. Relying on a final penetration test or manual pull request reviews is like trying to inspect every brick after the skyscraper is already built. It’s slow, wildly inefficient, and completely misses problems in the foundation. A single bad brick can compromise the entire structure.
Shifting Security Left with OWASP
To have any chance of keeping up, teams have to embrace a "shift left" mentality. This just means pulling security into the earliest stages of development—right when the code is being written. Security becomes something you do continuously, not a gate you have to pass at the end.
This is where the principles behind OWASP secure coding practices become your secret weapon. The OWASP framework gives everyone a battle-tested guide to spotting and fixing the most common and dangerous software vulnerabilities. It provides a common language for developers and security folks to talk about risk.
The trick is to stop seeing OWASP as a restrictive checklist and start using it as an essential guide. It empowers developers to be the first line of defense, catching and fixing issues in real-time as they code.
This isn't just a "nice-to-have" anymore. It's critical for any team that wants to build and ship software quickly and safely. In a world where AI-driven development is the new norm, OWASP provides the timeless wisdom we need to make sure faster code is also safer code. This guide will show you exactly how to put these principles into practice.
When most developers hear "OWASP," their mind immediately jumps to a long, scary list of security rules. It feels like a compliance checklist, a bunch of "don'ts" handed down from the security team.
But that completely misses the point. The Open Worldwide Application Security Project (OWASP) isn't about telling you what you can't do. It's a blueprint for building a fortress.
Think about it. You wouldn't build a bank vault by just throwing up some walls and hoping for the best. You'd use proven architectural plans that specify the steel thickness, the lock complexity, and sensor placement—all before laying a single brick. That’s exactly what OWASP secure coding practices are: a set of battle-tested principles for designing secure software from the very first line of code.
More Than Just a List of Dangers
The real magic of OWASP is that it's a living project, constantly updated by thousands of security pros, researchers, and developers who are in the trenches every day. They pool their knowledge of real-world attacks to create a shared language around security.
This means a developer in one country, a security analyst in another, and a project manager can all talk about a “Broken Access Control” issue and know they’re talking about the exact same thing. That shared understanding is the foundation of any real DevSecOps culture. It stops security from being some mysterious, niche field and makes it a transparent, team effort.
OWASP's goal isn't to create more security gatekeepers. It’s to empower developers to be the first line of defense by giving them the knowledge and tools to spot and stop threats as they build.
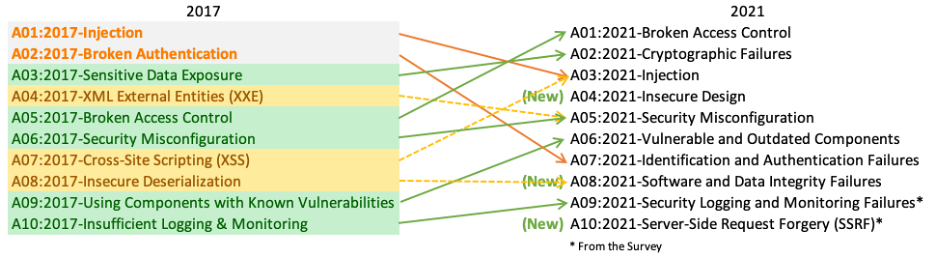
Because it's community-driven, the guidance actually stays relevant. The threats we face today are wildly different from a decade ago. For example, the famous OWASP Top 10 now includes risks like Server-Side Request Forgery (SSRF) and Insecure Design, which have exploded with the rise of complex microservices and APIs.
The Evolving OWASP Top 10
The OWASP Top 10 is the project's best-known resource, a quick-reference guide to the ten most critical security risks for web apps. It’s not static; it evolves to address the messy reality of modern development, including:
- AI-Induced Vulnerabilities: AI coding assistants are great at generating code fast, but they can also churn out classic vulnerabilities if they aren't guided. The Top 10 gives you the exact framework you need to audit that code.
- Supply Chain Risks: No one builds from scratch anymore. Modern apps are assembled from countless third-party libraries. The “Vulnerable and Outdated Components” category directly tackles the nightmare of vetting all those dependencies.
- Architectural Flaws: The inclusion of "Insecure Design" drives home a critical point: security isn't something you can bolt on later. It has to be baked in during the architectural phase, long before the first feature is coded.
Ultimately, OWASP gives development, security, and operations teams a practical, actionable guide to work from. It helps everyone speak the same language, see the same risks, and work toward the same goal: building software that doesn't just work, but is fundamentally secure. It's the foundation you build resilient and trustworthy applications on.
How The OWASP Top 10 Shows Up In Your Daily Code
Let's be honest, the OWASP Top 10 can feel a bit... abstract. It’s a list of scary-sounding threats that seem distant from the code you’re writing right now. But these aren't just theoretical problems for security researchers; they pop up in the everyday code you and your AI assistant generate.
The real trick to mastering secure coding practices owasp is learning to spot these vulnerabilities in your own work. It’s about turning those high-level concepts into tangible, fixable mistakes you can recognize on sight.
Think of OWASP as the blueprint for a digital fortress. It’s not just a list of rules but a shared language and foundation for building software that can actually withstand an attack.

So, let's break down how these fortress walls crumble in real-world scenarios.
The API That Trusted Any URL
One of the sneakiest and most common vulnerabilities today is Server-Side Request Forgery (SSRF), which you'll find under A10:2021. Imagine you’re building a simple feature to let users upload a profile picture by providing a URL.
It seems straightforward:
- A user gives you a link, like
http://example.com/image.jpg. - Your server fetches the image from that URL.
- You save it and display it. Done.
But what if a bad actor provides an internal URL instead, like http://127.0.0.1/admin/delete-all-users? If your server blindly trusts and fetches any URL it’s given, it might just execute that command on itself. That’s SSRF in a nutshell—an attacker tricking your server into doing their dirty work.
This isn't just a theoretical problem. Recent studies have shown just how often this crops up, especially in AI-generated code. In one analysis, SSRF was the single most frequent issue found, with 32 instances confirmed. It’s a perfect example of how even smart tools can miss fundamental security checks.
The Search Bar That Ran a Database Command
Here’s a classic: Injection (A03:2021). This vulnerability rears its head anytime you mix untrusted user input with commands or queries. A perfect illustration is a possible security issue related to SQL Server that shows how this plays out in the real world.
Think about a basic product search. A user types "jeans," and your code might build a SQL query like this: SELECT * FROM products WHERE name = 'jeans'.
The problem starts when an attacker types something malicious, like ' OR 1=1; --. Your code might naively construct this query: SELECT * FROM products WHERE name = '' OR 1=1; --. Suddenly, you're not searching for an empty string; you're telling the database to return every single product. A tiny coding error just turned into a massive data breach.
The Feature Flag Left On in Production
Security Misconfiguration (A05:2021) is a huge, critical category. This isn't about a single bad line of code, but the environment it runs in. It’s about the mistakes you make setting up your application, frameworks, or cloud services.
We’ve all seen it happen:
- Leaving default passwords active on a database or admin dashboard.
- Showing detailed error messages with full stack traces to users, giving attackers a perfect roadmap of your system.
- Forgetting to turn off a feature flag that enables a "debug mode" in your production environment.
These mistakes are often the path of least resistance when you're under a deadline. They're silent killers because they don't crash your app—they just leave the front door wide open for anyone to walk through.
The common thread here is trust. Insecure code trusts user input, it trusts default settings, and it trusts that networks are safe. OWASP-driven secure coding is about getting rid of that trust and verifying everything.
To put this in perspective, here's a table that connects these simple mistakes to the serious business consequences they can cause.
OWASP Top Vulnerabilities and Their Real-World Impact
This table maps some of the most common OWASP categories to everyday developer scenarios and their potential fallout. It's a stark reminder of why these "small" mistakes matter so much.
| OWASP Category | Common Scenario ('The Mistake') | Potential Business Impact |
|---|---|---|
| A03: Injection | Using raw user input to build a database query for a search feature. | Data breach, unauthorized access to all customer records, reputational damage. |
| A05: Security Misconfiguration | Deploying an application to production with a cloud storage bucket left publicly accessible. | Sensitive data exposure, regulatory fines (GDPR, CCPA), loss of customer trust. |
| A10: Server-Side Request Forgery | Building a webhook that fetches data from any URL a user provides without validation. | Internal network scanning, access to internal services, potential full system compromise. |
Seeing the direct line from a line of code to a data breach or a massive fine makes it clear: these aren't just abstract security concepts. They are business risks that we, as developers, have the power to prevent.
Practical Mitigation Strategies and Code Examples

Knowing the threats is one thing. Writing code that actually stops them is another. Let's move past the theory and get our hands dirty with concrete, code-level fixes for some of the biggest OWASP vulnerabilities. The goal here is simple: give you battle-tested patterns you can start using today.
We'll look at vulnerable code side-by-side with its secure counterpart. Seeing the "before" and "after" makes it crystal clear how a few key changes can transform a security hole into a hardened feature. These examples prove that security isn't some abstract art—it’s a skill built on applying the right techniques at the right time.
Defeating Injection With Parameterized Queries
SQL Injection is still one of the most dangerous vulnerabilities out there. Why? Because it gives attackers a direct line to your database. It happens when you take untrusted user input and stitch it directly into a database query.
Vulnerable Code Snippet (Python)
Imagine a simple search function. If you just slap the user's input into the SQL string, you're building a backdoor for attackers. This is a disaster waiting to happen.
import sqlite3
def find_products(search_term): conn = sqlite3.connect("database.db") cursor = conn.cursor()
DANGEROUS: String formatting creates a SQL injection vulnerability
query = f"SELECT * FROM products WHERE name = '{search_term}'" cursor.execute(query) results = cursor.fetchall() conn.close() return results
An attacker could just type '; DROP TABLE users; -- into the search box and potentially wipe out your entire user table. Game over.
Secure Code Snippet (Python)
The fix is a hard and fast rule: never mix code and data. Use parameterized queries (or prepared statements) instead. This sends the query structure to the database first, and the user's data separately.
import sqlite3
def find_products_secure(search_term): conn = sqlite3.connect("database.db") cursor = conn.cursor()
SECURE: Parameterized query separates the query from the data
query = "SELECT * FROM products WHERE name = ?" cursor.execute(query, (search_term,)) results = cursor.fetchall() conn.close() return results
In the secure version, the database engine knows that search_term is just data. It's never treated as an executable command, shutting down the attack completely. While this handles the application logic, remember that a strong defense also requires solid database security best practices.
Neutralizing SSRF With Allowlists
Server-Side Request Forgery (SSRF) is a sneaky attack that tricks your server into making network requests on the attacker's behalf, often to poke around your internal systems. This happens anytime your application takes a URL from a user without checking where it actually goes.
Vulnerable Code Snippet (JavaScript/Node.js)
Let's say you have a feature that fetches an image from a URL someone provides. Without any checks, it becomes a tool for an attacker to scan your private network.
const express = require('express'); const axios = require('axios'); const app = express();
app.get('/fetch-image', async (req, res) => { const { url } = req.query; // DANGEROUS: The server fetches any URL provided by the user try { const response = await axios.get(url); res.send(response.data); } catch (error) { res.status(500).send('Error fetching URL'); } });
An attacker could just pass in url=http://127.0.0.1:8080/internal-api and start probing for services that should be completely hidden from the outside world.
SSRF is especially nasty because it turns your own application into a proxy for the attacker. The absolute best defense is a strict allowlist. Don't try to block bad URLs; only define the good ones.
Secure Code Snippet (JavaScript/Node.js)
Instead of playing whack-a-mole with a blocklist, you should explicitly define what's allowed. This "deny by default" approach is a core principle of secure coding practices owasp.
const express = require('express'); const axios = require('axios'); const { URL } = require('url'); const app = express();
const ALLOWED_DOMAINS = ['trusted-images.com', 'cdn.example.com'];
app.get('/fetch-image-secure', async (req, res) => { const { url } = req.query; try { const parsedUrl = new URL(url); // SECURE: Check if the hostname is in the allowlist if (!ALLOWED_DOMAINS.includes(parsedUrl.hostname)) { return res.status(400).send('Forbidden host'); }
const response = await axios.get(url); res.send(response.data); } catch (error) { res.status(500).send('Error processing request'); } });
Context Matters Language and Training
The language you choose can also stack the deck for or against you, especially when using AI to generate code. One analysis showed a GPT model producing vulnerable code 11.4% of the time in Python, but that number jumped to a much riskier 26.7% in JavaScript. That’s a huge gap, and it highlights how inconsistent AI training can be across different languages.
Adopting fundamental OWASP secure coding patterns—like using parameterized queries and strict allowlists—is the great equalizer. It dramatically lowers these risks, no matter who or what is writing the code. You can find more of these kinds of insights on AppSec Santa.
This just reinforces that secure coding isn't about one tool or language. It’s about applying universal, defensive principles to your work. These patterns are your best weapons for hardening code, whether it was written by you, a teammate, or an AI assistant.
Integrating OWASP into Your Development Workflow
Let’s be honest: secure coding practices are useless if nobody follows them. If security feels like a chore or a roadblock, developers will—quite rightly—find a way to work around it. The only way to make it stick is to weave OWASP principles directly into the day-to-day grind, so security becomes less of a gatekeeper and more of a helpful partner.
This isn't about more manual pull request reviews or waiting for the annual pen test report. The whole game has changed. Today, it’s about embedding security checks into every single stage of development, a concept people often call DevSecOps. It’s how you make secure coding practices owasp an automatic reflex, not an afterthought.
Shift Left with In-IDE Feedback
The best time to fix a security flaw is the second it’s written. That’s the whole idea behind the "shift left" philosophy, and it comes to life with tools that plug directly into your IDE. If you’re not familiar with the concept, it’s worth understanding the power of shift-left security testing.
Think of these tools as a spell-checker, but for security vulnerabilities. As you or your AI assistant crank out code, these extensions are watching in the background, flagging potential OWASP Top 10 violations on the fly. That immediate feedback loop is a game-changer.
- Instant Learning: Instead of getting a security ticket a week later, you see the mistake right away and learn how to fix it on the spot.
- Reduced Friction: It kills the painful back-and-forth that happens when a security issue blocks a PR for hours or even days.
- Pre-Commit Prevention: Vulnerabilities get squashed before the code ever gets committed, which drastically cleans up the security of your entire codebase from the ground up.
This is especially critical for teams relying on AI coding assistants. Real-time checks in the IDE are a must—it’s what we do at kluster.ai, scanning 100% of AI-generated code in seconds. We enforce OWASP-aligned guardrails to catch things like SSRF, injections, and misconfigurations before they even have a chance to hit the repository. Without that safety net, you’re just shipping vulnerabilities at scale. The data on this is pretty clear, as you can see in the AppSec Santa research.
Automate Security in Your CI/CD Pipeline
While the IDE is your first line of defense, the CI/CD pipeline is your automated security checkpoint. By plugging security scanners in here, you build guardrails that physically prevent vulnerable code from making it to production. This automated workflow usually has a few different layers of scanning.
Security automation doesn't replace developers; it empowers them. By handling the repetitive checks, it frees up developers to focus on building great features, confident that a safety net is in place.
Here’s a breakdown of how the different scanners fit into your pipeline:
-
Static Application Security Testing (SAST): A SAST tool is like a linter for security. It scans your source code without actually running it, and it's fantastic at finding common OWASP issues like SQL injection, hardcoded secrets, or bad configurations. They run fast and can be set up to fail a build if anything critical pops up.
-
Software Composition Analysis (SCA): Let's face it, most of our apps are just a collection of open-source libraries glued together. SCA tools scan all your dependencies, compare them against databases of known vulnerabilities (CVEs), and scream if you’re using a package that’s old or compromised. This is your defense against OWASP A06:2021-Vulnerable and Outdated Components.
-
Dynamic Application Security Testing (DAST): Unlike SAST, a DAST tool tests your application while it's actually running. It basically acts like an automated hacker, poking and prodding your app from the outside to find things like Cross-Site Scripting (XSS) or Broken Access Control that you can only spot in a live environment.
When you combine real-time feedback in the IDE with these automated checks in the pipeline, you create a seriously tough, multi-layered defense. This approach makes secure coding a natural part of getting things done, cutting down on review bottlenecks and letting your team ship code that’s both innovative and solid.
Building a Lasting Culture of Security
Let's be real: buying a bunch of security tools won't make you secure. IDE scanners and CI/CD pipelines are great, but they’re just one piece of the puzzle. If you want real, lasting resilience, you need a culture where security is everyone's job, not just a problem for the security team to clean up.
This doesn't happen by accident. It’s a deliberate shift to make security a core part of your team's DNA. It needs to show up in daily stand-ups, sprint planning, and even performance reviews. You have to stop treating security as a checkbox and start treating it as a measure of quality.
The goal is to get to a place where developers are your first line of defense—not because they have to be, but because they want to be. When building secure code becomes a point of pride, you’ve won.
This isn’t about adding more process. It's about creating a system where writing secure code is simply the easiest and most logical way to work.
Establish Automated Security Guardrails
First things first: you need a safety net. This isn't about catching developers making mistakes; it's about giving them instant, useful feedback right when they need it, before a problem ever gets committed.
- Standardize In-IDE Tooling: Get every single developer on the same real-time security tools inside their editor. This creates a consistent standard and stops vulnerabilities at the source.
- Mandate CI/CD Security Gates: Set up your pipeline to automatically block any PR that introduces a high-severity vulnerability. Make it a non-negotiable rule. If the code isn't secure, it doesn't ship. Period.
- Automate Dependency Scanning: Use tools that constantly watch your open-source packages. When a new vulnerability pops up in a library you’re using, your team should know immediately.
The data here is screaming for this. Recent research from AppSec Santa shows that for engineering managers, automated enforcement in the IDE is the key to cutting review times in half and shipping safer code. The numbers don't lie.
Champion Practical Training and Audits
Next, you need to make training stick. Forget the once-a-year, generic security presentation that everyone tunes out. Education has to be practical, continuous, and relevant to the code your team is actually writing.
When you find a new vulnerability, don’t just fix it. Turn it into a teaching moment. Show the whole team the bad code, walk them through the fix, and have a real conversation about how to avoid it in the future. Use your own codebase as the textbook.
You also need to formalize how you review code. Ad-hoc checks are unreliable. You need clear guidelines for what a solid security review actually looks like. If you need a starting point, our guide on structuring effective security code reviews breaks it down. Auditing your own practices keeps everyone honest and ensures the standards you set are actually being met.
Ultimately, building a security-first culture is a massive competitive advantage. It translates directly to faster releases, fewer costly incidents, and customers who actually trust your product. By putting automated guardrails in place and championing practical, hands-on education, you give your team the power to build and ship with confidence.
Frequently Asked Questions About OWASP Practices
When you're trying to get a handle on secure coding, a lot of questions pop up. It's easy to get lost in the jargon. Let's cut through the noise and get straight to what you actually need to know about applying OWASP standards.
How Often Should We Review Code Against The OWASP Top 10?
The only real answer is: all the time. The old way of doing security—periodic, manual code reviews—is completely broken in a world of CI/CD. It’s slow, expensive, and it misses most of the issues.
Instead of thinking of security as a special event, you need to bake it into your daily workflow. This means using automated security scanning (SAST) right in your CI/CD pipeline and, even better, putting real-time security tools directly into every developer's IDE.
This flips the model completely. Every single commit gets checked automatically. Security stops being a bottleneck and becomes a background habit.
The goal is to make security a continuous, automated process, not a periodic checklist. When you have real-time checks in the IDE and CI pipeline, writing secure code becomes the path of least resistance.
Is Following The OWASP Top 10 Enough For Full Application Security?
No, but it's absolutely where you have to start. The OWASP Top 10 isn't just a random list; it's an inventory of the most common and destructive vulnerabilities applications face in the wild. It’s the application security version of the 80/20 rule—fix these ten things, and you've eliminated a massive chunk of your risk.
But a truly solid security posture is built in layers. Just like you wouldn't rely on a single lock to protect a bank vault, you can't rely on just the Top 10. A mature security program also includes:
- Secure Design and Threat Modeling: Thinking about security before you even write the first line of code.
- Dependency Scanning (SCA): Making sure the third-party libraries you pull in aren't hiding known vulnerabilities.
- Infrastructure Security: Locking down the servers, containers, and services that run your application.
Think of the Top 10 as the strong foundation of your security strategy. It's essential, but it's not the entire building.
Where Should Teams Using AI-Generated Code Start With OWASP?
If your team is leaning heavily on AI coding assistants, you need to get laser-focused on the specific types of bugs these tools tend to create. Based on what we're seeing in real-world codebases, there are three areas that demand immediate attention:
- A03 Injection: AI models are notoriously bad at this. Make strict input validation and parameterized queries your highest priority. Don't trust any data coming from anywhere.
- A10 Server-Side Request Forgery (SSRF): These tools often generate code that makes outbound requests without proper validation. Implement strict allowlists for every single external call.
- A05 Security Misconfiguration: AI often falls back on default settings, which are almost always insecure. Every configuration needs to be set explicitly and hardened.
These three vulnerabilities represent the most frequent security holes in AI-generated code. Start here, and you'll be tackling the biggest risks first.
Ready to eliminate security bottlenecks and ship trusted AI-generated code? kluster.ai provides real-time, in-IDE security checks to catch vulnerabilities before they ever leave the editor. Bring automated OWASP guardrails and organizational standards to every developer's workflow. Start free or book a demo at https://kluster.ai.